Introduction
Linux is a UNIX-like computer operating system developed and distributed under the free and open source software concept.
The defining component of any Linux system is the Linux kernel, an operating system kernel first released on September 17, 1991, by Linus Torvalds.
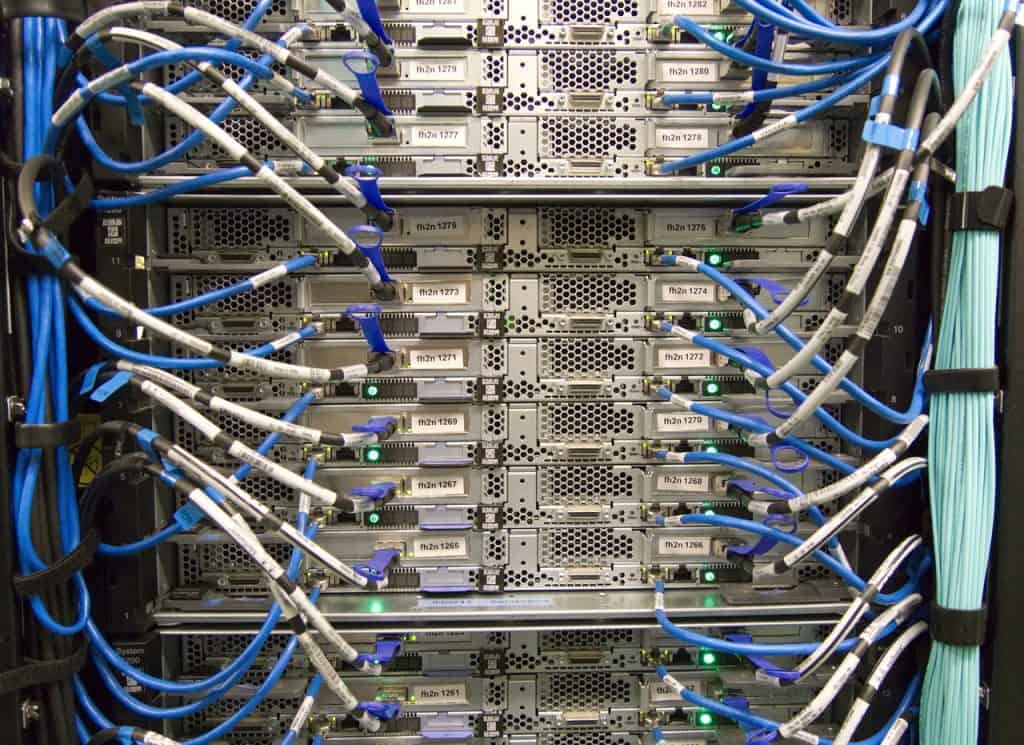
Linux systems are widely used in many industries, from personal computers (PCs) to the servers that form the backbone of the Internet. Linux is also used in embedded systems, such as cell phones, routers, and video game consoles.
You may use Linux to implement numerous layers of security in your Linux server environment.
The sections that follow will lead you through the server software packages that you might encounter while implementing Linux security features.
In this article:
- Authentication Server
- NIS
- Kerberos
- LDAP
- Certificate Authority
- SSH
- Virtual Private Networks
- Proxy Server
- Monitoring
- Important exam notes
- Exam questions
Authentication Server
The first thing that any would-be user of a Linux system must do is identify themselves to the system. This is done via a process called authentication, which is the process of verifying the identity of a user.
The most common form of authentication is to use a username and password, although other methods, such as public key authentication, are also available.
Once the user has been authenticated, the system can then determine what level of access to give the user. This is done via a process called authorization, which is the process of granting or revoking access to system resources.
There are two main types of authorization in Linux: file permissions and process permissions. File permissions control who can read, write, and execute files, while process permissions control who can kill processes and change their priority.
The /etc/passwd and /etc/shadow files record the user name and password. Each Linux server keeps track of the legitimate user accounts that have access to the machine.
Trying to remember many userids and passwords in a large network environment where users may need to access resources on multiple Linux servers can be difficult.
For sharing user account databases across several Linux servers on a network, there are a few options.
NIS
Linux systems can be configured to use Network Information Service (NIS), also known as Yellow Pages (YP), for user authentication. NIS is a client-server system that allows a central server to manage the user accounts on a network of Linux systems.
When a user tries to log in to a Linux system that is configured to use NIS, the system contacts the NIS server and attempts to authenticate the user.
On local networks, the NIS naming directory is frequently used as a central repository for user accounts, hostnames, and even email information.
Linux systems can also be configured to use Network Information Service Plus (NIS+), which is an updated version of NIS.
The nis-utils package is an open-source project that allows you to set up a NIS or NIS+ directory on Linux. Most Linux distribution repositories have it.
Kerberos
Linux systems can also be configured to use Kerberos for user authentication.
Kerberos is a secure authentication technology created at MIT. Users are securely authenticated with a centralised server database using symmetric-key cryptography. Because the entire authentication procedure is encrypted, it’s a safe way to log into a Linux server.
The Kerberos authentication system can be used for more than server logins. Many popular Linux server programmes provide plug-in modules that connect to a Kerberos database for user authentication.
LDAP
OpenLDAP is a free and open-source implementation of the Lightweight Directory Access Protocol.
Lightweight Directory Access Protocol (LDAP) is an industry-standard protocol for accessing and maintaining distributed directory information services over an Internet Protocol network.
OpenLDAP provides a suite of LDAP-related applications and utilities, including slapd(8), the stand-alone LDAP daemon; slurpd(8), the stand-alone LDAP replication daemon; and many utilities.
OpenLDAP allows you to create a hierarchical database for storing network objects. Objects in a hierarchical database are connected to one another in a treelike pattern.
You can arrange objects in hierarchical databases by type, such as users and servers, or by location, or both. This gives you a lot of flexibility when it comes to designing authentication for your local network.
Both client and server programmes are included in the OpenLDAP package. The client programme enables systems to communicate with an OpenLDAP server in order to authenticate requests from clients and other network objects.
Certificate Authority
A certificate authority is an entity that issues digital certificates. A digital certificate certifies the ownership of a public key by the named subject of the certificate. This allows others (relying parties) to rely upon signatures or on assertions made about the private key that corresponds to the public key.
A certificate authority issues certificates according to a certificate policy, which is usually expressed in an Internet Security Glossary – Certificate policy or Certification practice statement.
Sharing user accounts, simple passwords, and even accounts with default passwords are all security risks when using the userid/password method of login into a server.
Certificates are a superior way of authenticating users. A certificate is a digitally signed key that enables two-factor authentication.
For both servers and clients, the OpenSSL package provides standard certificate services. You can configure your Linux server to generate certificates for clients, which you can then use to authenticate them with network apps.
SSH
SSH (Secure Shell) is a secure protocol and the most common way of safely administering remote servers. The main function of this protocol is to provide secure access to a remote computer. It also supports file transfers and tunneling.
SSH is a command-line tool that allows you to connect to a remote computer and execute commands. SSH is normally used to log into a remote machine and execute commands, but it also supports tunneling, forwarding arbitrary TCP ports and X11 connections.
It’s not a smart idea to log into a server using a plaintext protocol like Telnet or FTP from a remote location.
The Secure Shell (SSH) adds an extra layer of security to data exchanged over the internet.
The OpenSSH package is the most widely used SSH implementation in the Linux environment. The OpenSSH programme uses SSH to provide secure Telnet, FTP, and even remote copying.
Tunneling allows you to encrypt any type of network transaction, securing any type of network application even if it isn’t directly supported by the OpenSSH software.
Virtual Private Networks
VPN is a technology that creates a private tunnel over the internet between two devices, usually your computer and the server of a service you wish to access.
The Virtual Private Network (VPN) protocol is used to connect to resources on a local network from a remote. A secure point-to-point tunnel is established between a remote client or server and a VPN server on your local network using the VPN protocol. This gives you a safe way to access any server on your local network from remote.
The OpenVPN is the most common VPN option on Linux.
On a Linux server on your company network, the OpenVPN package operates as a server service. Remote clients can connect to the OpenVPN server using OpenVPN to establish connectivity to the server and then obtain access to the rest of your local network once on the server.
Proxy Server
A proxy server is a server that acts as an intermediary between a client and another server. A proxy server forwards requests between clients and servers. If a client connects to a server through a proxy server, then the client’s IP address will be hidden from the server.
You can intercept web requests from local network clients using a web proxy server. You can regulate how clients interact with remote web servers by intercepting web requests.
The web proxy server can block websites that you don’t want your network customers to see, and it can cache popular websites to speed up future requests for the same pages.
The Squid package is the most popular web proxy server in Linux.
It can be set up to function as both a filter and a cache server. The nginX web server package, may also act as a web proxy server and is gaining popularity.
Monitoring
Keeping track of what your Linux servers are doing might be difficult if you have numerous of them on your network. System administrators should always keep an eye on a server’s performance and log files to see whether anything unauthorized is happening.
In the Linux ecosystem, there are a variety of monitoring tools. The Nagios software package is increasingly gaining popularity, particularly in cloud Linux environments.
Nagios monitors the performance and logs of Linux servers using SNMP and displays the findings in a simple graphical panel.
Important exam notes
Explain the main ways in which you can launch server programmes under Linux.
In Linux, server programmes can either operate in the background as a daemon process or be started from a super-server daemon when a client requests it.
Describe how clients are able to communicate with a server application.
On well-known ports, server applications listen for client connections. Clients must make a connection request to the server on the application’s well-known port.
Describe the elements that make up a LAMP stack.
The LAMP stack provides a framework for web applications by combining the Linux operating system, Apache web server, MySQL database server, and PHP programming language.
the methods through which a Linux server can transfer files over a local network
The nfs-utils package allows Linux servers to connect with one other and share files through NFS. Folders from the remote Linux server can be mounted on the local Linux server as if they were local discs. Samba allows Linux servers to exchange files on Windows local networks with Windows clients and servers, as well as map folders on Windows servers.
On a local network, what server packages are often used to implement network features?
The DHCPd package provides DHCP server functions, which allow clients to be assigned IP addresses. For hostname resolution, the BIND package provides DNS server services to both clients and servers on a local network. You can use the net-snmp package to provide SNMP-based remote device management, and the ntpd package to establish an NTP time server for your local network.
Describe how to use Linux to establish a network directory server.
The OpenLDAP software allows you to establish an LDAP directory of local network users and devices. The LDAP directory can be used by clients and other servers to authenticate individuals and devices on the network.
Exam questions
- In the popular LAMP stack, which web server is used?
- nginX
- Apache
- Lighthttpd
- PostgreSQL
Answer:
B. The LAMP stack, which consists of the Apache web server, the Linux, MySQL, and PHP, has grown in popularity. The Nginx web server is a newer webserver that is gaining popularity, however, it is not included in the LAMP stack. Because of its modest memory and CPU footprint, the Lighthttpd web server is appropriate for embedded computers but not for large-scale LAMP applications. PostgreSQL is a database server rather than a web server.
- For a single application, which one of the below runs in the background and listens for client connection requests?
- Daemon
- Super-server
- Shell
- Graphical desktop
Answer:
A. a daemon is a application that operates in the background and listens for client connection requests. A super-server is a server that listens for multiple applications. The shell does not wait for network connections to open; instead, it runs apps in real time. You can also launch applications from the graphical desktop, but it does not listen for client connection requests.
- Which open-source database is popular for web applications because of its rapid performance?
- MongoDB
- PostgreSQL
- MySQL
- NoSQL
Answer:
C. The MySQL database server was designed with speed in mind when it was initially released, making it popular. The MongoDB database server offers object-oriented database functionality without a performance priority. Instead of focusing on speed, the PostgreSQL database concentrated on creating complex database capabilities. NoSQL is a database storage mechanism that uses object-oriented data records, rather than a database server package.
- How does a server know which application daemon receives which client request?
- IP addresses
- Ports
- Ethernet addresses
- Services
Answer:
B. Linux services monitor well-known ports for client requests. To handle numerous apps, a server usually has a single IP address. In most cases, the server has only one Ethernet address. Individual services on the server cannot be launched by clients.
- Which well-known open source web server can also act as a load balancer?
- nginX
- Apache
- PostgreSQL
- Lighthttpd
Answer:
A. Client requests can be routed to several backend web servers using the nginX web server as a load balancer. This feature is not supported by the Apache and lighthttpd web servers.